How is Cyber Shaping the Insurance Industry? Learn From Pros at Allstate, Trustmark and BCSF
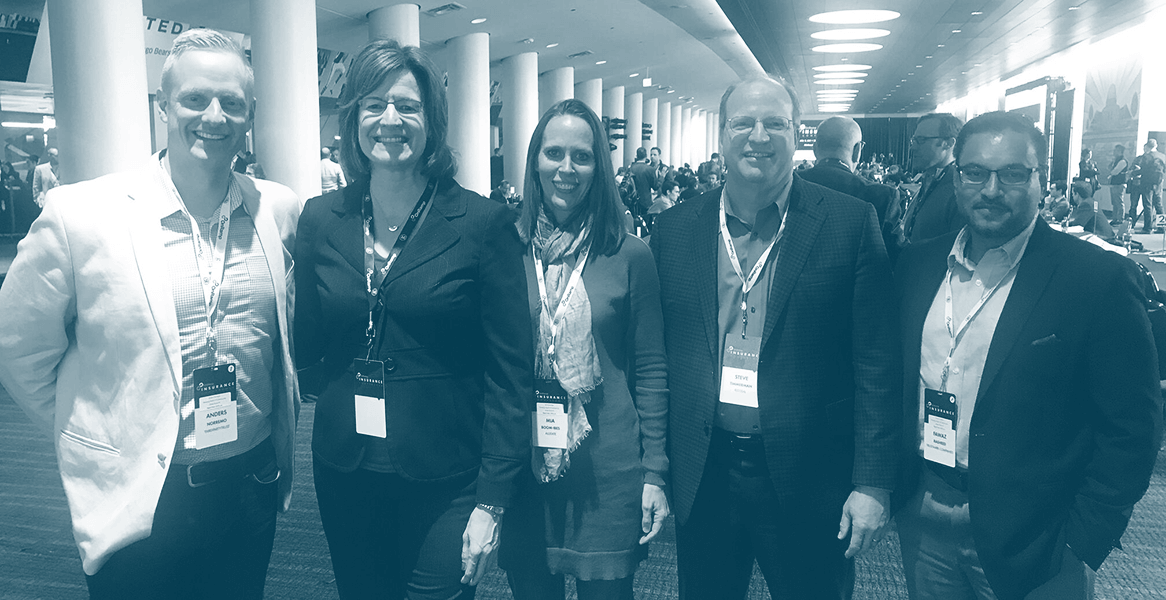
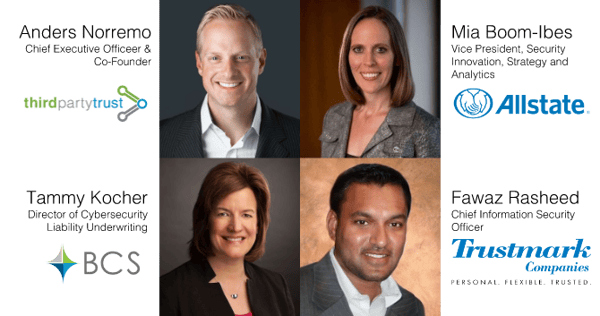
Anders Norremo, CEO of ThirdPartyTrust, had the pleasure of moderating a panel at the OnRamp Insurance Conference on Thursday April 12th, 2018. The panelists included Mia Boom-Ibes, Fawaz Rasheed, Steve Timmerman, and Tammy Kocher. They all gave great insight to how cybersecurity is shaping the insurance industry.
We will explore questions surrounding the New York Department of Financial Services Cyber Regulation, next-generation technologies and the biggest needs from these organizations.
WHAT’S AT THE FOREFRONT OF CYBERSECURITY? AND HOW IS IT IMPACTING business STRATEGY?
Fawaz Rasheed, the CISO of Trustmark, started out by providing three areas at the forefront of his firm, which operates with $2.2B in assets and ranges across state and business lines.
- Regulation – it impacts our offerings and business operations concretely.
- Customers are mandating we have controls in place.
- Cybersecurity has risen to the board level, where discussions are being had about “How confident are we that we can detect a breach?”
Mia Boom-Ibes adds finding resources and people to do the cybersecurity jobs is a struggle. In an industry that is rapidly changing like car insurance, she is tasked with enabling change within the organization in a secure fashion and that starts with people. Tammy Kocher chimed in and says the threat landscape is changing daily and organizations, need to go back to the basics. They need better training, people awareness and accountability.
HOW IS THE NEW YORK DEPARTMENT OF FINANCIAL SERVICES CYBER SECURITY REGULATION IMPACTING YOUR ORGANIZATIONS?
Boom-Ibes said, “It’s about time. The insurance industry hasn’t been regulated in the past.” It’s about time regulators have basic expectations around security. She described a great place to start for insurance companies – “What systems matter to you? and then assess that. And ask what controls should I put into place?” Kocher adds, “It’s only good, if you have security become part of your culture.”
Rasheed describes his conversations about the New York Cyber Security Regulation and uses the analogy of home security. “Homeowners have to invest in security protection to ensure every window, door and opportunity is safeguarded. If one door is unlocked at night that’s all a criminal needs to break-in.” The same theory applies for cyber security. He says states are starting to understand a layered concept. He says “Regulators are mandating a layered approach because they are starting to understand it’s the best approach to securing the house.”
He also added some wise words:
“I don’t own the risk, I govern the risk. The board owns it.”
HOW ARE YOU ENABLING THE PEOPLE TO DO THEIR JOBS, WHILE KEEPING YOUR COMPANY SAFE?
Boom-Ibes is the VP of Security Innovation, Strategy and Analytics and this is her job. She states, “We need to enable businesses to move. Move with the speed of agile development and enable the necessary skills our people need.” She dove deeper and explained how Allstate has a lab to address vulnerabilities in the connected car.
Rasheed adds, “Security needs to be frictionless.” Frictionless seemed to be the resounding theme of each of the panelists comments. Timmerman adds that throughout his career, security has always been part of innovation and continues to be today.

WHAT ARE SOME OF THE NEW COOL TRENDS IN CYBER SECURITY YOU ARE SEEING?
Tammy from BCSF says there’s a lot of opportunity for tools that help quantify how much financial risk they, if there is business interruption. She also believes there to be opportunity in reward based phishing tools focused on improving the perception of security. Rasheed adds, “Attackers are trying to stay one step ahead. It’s really a matter of how to utilize artificial intelligence while traversing networks.”
To learn more about our platform, request your demo now: